How Are Asymmetric Keys Generated
My concept is that the application the users download to pull the files from the site will also allow them to generate the keys for use on the site. So my question is, Is it possible to create an asymmetric private/public key pair based on a passphrase? This would allow the user to regenerate the private key if required. Asymmetric keys. RSA and ECC keys can be generated using the PKA Key Generate service. The RSA private keys can be generated within the secure boundary of the card and never leave the secure boundary. Only the domain that created the retained key can access it. Public-key cryptography, or asymmetric cryptography, is a cryptographic system that uses pairs of keys: public keys, which may be disseminated widely, and private keys,which are known only to the owner. The generation of such keys depends on cryptographic algorithms based on mathematical problems to produce one-way functions. Effective security. RSA (Rivest–Shamir–Adleman) is one of the first public-key cryptosystems and is widely used for secure data transmission. In such a cryptosystem, the encryption key is public and distinct from the decryption key which is kept secret (private). In RSA, this asymmetry is based on the practical difficulty of factoring the product of two large prime numbers, the 'factoring problem'. Apr 18, 2016 What make asymmetric ciphers “safe” is not the algorithm, key length or patents. It’s the ability to protect the Private Key. Once that Key is compromised the rest of the security flies out the window. Asymmetric Keys are only as secure as the infrastructure, the technology, and the human element used to protect them. Asymmetric key Depending on the type of cryptographic system used, the public key is obtained from an encryption of the private key or vice versa. For example, the public key that you use to transfer your bitcoins is created from the private key by applying a series of a cryptographic hash. Nov 29, 2016 Asymmetric Cryptography, also known as Public Key Cryptography, is an encryption system in which two different but uniquely related cryptographic keys are used.The data encrypted using one key can be decrypted with the other. These keys are known as Public and Private Key Pair, and as the name implies the private key must remain private while the public key can be distributed.
Cryptography
Derrick Rountree, in Security for Microsoft Windows System Administrators, 2011 /skyrim-pc-cd-key-generator.html.
Asymmetric Encryption
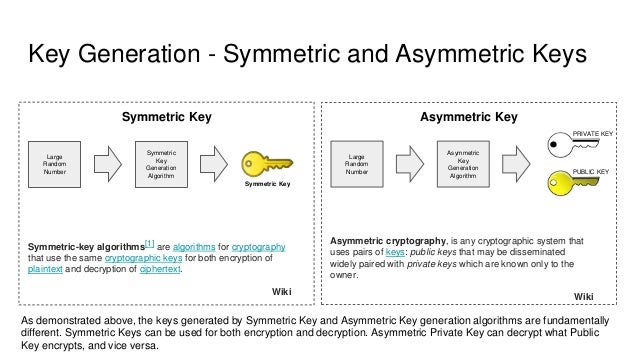
Asymmetric encryption is also referred to as public key encryption. In asymmetric encryption, both the encrypting and decrypting systems have a set of keys. One is called the public key, and another is called the private key. If the message is encrypted with one key in the pair, the message can be decrypted only with the other key in the pair.
Asymmetric key algorithms are not quite as fast as symmetric key algorithms. This is partially due to the fact that asymmetric key algorithms are generally more complex, using a more sophisticated set of functions.
Asymmetric Key Algorithms
Asymmetric key algorithms aren't as widely used as their symmetric counterparts. So we'll just go over two of the big ones: Diffie-Hellman and RSA.
Diffie-Hellman: The Diffie-Hellman algorithm was one of the earliest known asymmetric key implementations. The Diffie-Hellman algorithm is mostly used for key exchange. Although symmetric key algorithms are fast and secure, key exchange is always a problem. You have to figure out a way to get the private key to all systems. The Diffie-Hellman algorithm helps with this. The Diffie-Hellman algorithm will be used to establish a secure communication channel. This channel is used by the systems to exchange a private key. This private key is then used to do symmetric encryption between the two systems.
RSA: It is the Rivest Shamir Adelman algorithm. RSA was developed in 1978. RSA was the first widely used asymmetric algorithms used for signing and encryption. It supports key lengths of 768 and 1,024 bits. The RSA algorithm uses a three-part process. The first part is key generation. The keys used in the RSA algorithm are generated using mathematical operations based on prime numbers. The second part of the process is encryption. This encryption is done using one of the keys in the key pair. The third part of the process is decryption. The decryption is done using the other key in the key pair.